| Version 18 (modified by , 10 years ago) (diff) |
|---|
Configure OVS With Layer 3 Routing
Open vSwitch (OVS) acts as a Layer 2 device when it's not connected to its controller (and its fail-safe-mode is set to standalone [default]). If we want to do Layer 3 control, we need to write the control logic in its controller. However, sometimes we want to Layer 3 control while there is other Layer 3 control. For example, we want to do firewall or NAT while there is IP routing managed by XORP or Kernel Static Routing. A straightforward solution is to write your own IP forwarding logic in your controller (Yeah, practice of writing your own XORP is fun!). This is really violating the reusability principle of software engineering. Another solution is to cross your finger and hope there is someone has written it for the controller framework you use.
In this page, we are going to show you how to configure OVS to work with Linux kernel static IP routing. The method is largely from the help of Ryan Izard, rizard@g.clemson.edu, from Clemson University.
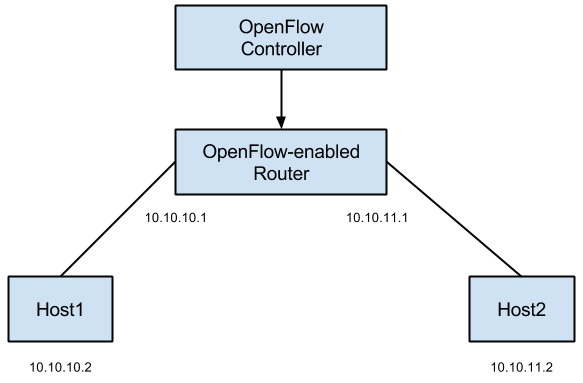
The topology we want to have is shown in below figure.
The configuration we want to have is shown in below figure.
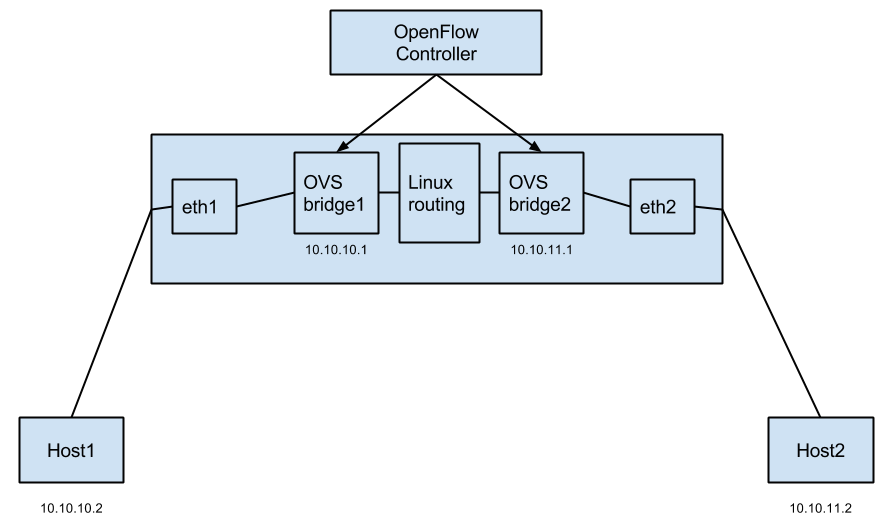
In summary the idea is to create a single OVS bridge for each interface on your machine that you want to assign an IP; pass the packet between the interface and the network stack through the LOCAL port of OVS; and let Linux routing handle the rest of the part. This wiki page provides step-by-step instructions.
We've generated a RSpec http://groups.geni.net/geni/raw-attachment/wiki/HowTo/ConfigureOVSWithLayer3Routing/ovs-l3-routing.rspec for you to try it out before applying it to your topology. You need to reserve it and login to host OVS to configure.
- Create 2 OVS bridges.
ovs-vsctl add-br OVSbr1 ovs-vsctl add-br OVSbr2
- Zero out the IP of interfaces as you will assign it to the OVS bridges (your interface names may vary). On GENI, be careful not to bring down eth0, because it is your control interface, if you bring that interface down you won't be able to login to your host!
ifconfig eth1 0 ifconfig eth2 0
- Attach interfaces to according OVS bridges. Again, don't attach control plane interface.
ovs-vsctl add-port OVSbr1 eth1 ovs-vsctl add-port OVSbr2 eth2
4.Verify the configurations by:
ovs-ofctl show OVSbr1
See output here.
ovs-ofctl show OVSbr2
See output here.
ovs-vsctl show
See output here.
- Assign the IP addresses to the OVS bridges, and add routing entries (clean up ones if needed).
ifconfig OVSbr1 10.10.10.1/24 up ifconfig OVSbr2 10.10.11.1/24 up
These will insert the corresponding routes automatically for you, and you can verify it via:
route -n
See output here.
Alternatively, you could do:
ifconfig OVSbr1 10.10.10.1 up ifconfig OVSbr2 10.10.11.1 up route add -net 10.10.10.0 netmask 255.255.255.0 dev OVSbr1 route add -net 10.10.11.0 netmask 255.255.255.0 dev OVSbr2 route -n
- When an OVS bridge is installed in the Linux OS, it is wired such that any application packets or packets routed via Linux will be sent to the LOCAL port of the OVS bridge, assuming a route to that bridge exists. And, in the reverse direction, any packets sent out an OVS bridge's LOCAL port will be received by the local networking stack.
Let's do an example of how a packet would traverse our network from 10.10.10.2 to 10.10.11.2.
10.10.10.2 sends the packet with destination 10.10.11.2. The packet arrives at eth1. There is an OpenFlow flow in place on OVSbr1 between eth1 and it's LOCAL port, so the packet will match this flow and be sent out the LOCAL port of OVSbr1 (i.e. port 65534). The packet is then received by the local machine's network stack. It has a destination IP of 10.10.11.2, so the routing table we have established will send the packet to the OVSbr2 network interface. OVSbr2 will receive this packet from the local network stack via it's LOCAL port (i.e. port 65534). There is an OpenFlow flow in place on OVS2 between OVS2's LOCAL port and eth2, so this packet will match that flow and be sent out eth2. From there, it will arrive at 10.10.11.2. The same process will occur in reverse. This assumes though that you insert the flows between the physical interfaces (eth1 and eth2) and the OVS LOCAL ports. That's the key to handing packet to and receiving packets from the local OS.
- If you want to insert these flows with OVS itself, you can do something like the following:
ovs-ofctl add-flow OVSbr1 in_port=port_number_of_eth1,actions=LOCAL ovs-ofctl add-flow OVSbr1 in_port=LOCAL,actions=output:port_number_of_eth1 ovs-ofctl add-flow OVSbr2 in_port=port_number_of_eth2,actions=LOCAL ovs-ofctl add-flow OVSbr2 in_port=LOCAL,actions=output:port_number_of_eth2
You can determine port_number_of_eth1 via:
ovs-ofctl show OVSbr1
According to output here, the port number of eth1 is 1.
- If you want to insert these flows via your controller, you will need to either specify port 65534 explicitly or use whatever convention your controller uses to specify the LOCAL port of a bridge.
Remember to set your controller to all OVS bridges you want to control:
ovs-vsctl set-controller OVSbr1 tcp:127.0.0.1:6653 ptcp:6634:127.0.0.1 ovs-vsctl set-controller OVSbr2 tcp:127.0.0.1:6653 ptcp:6634:127.0.0.1
- Apart from these, remember to verify IP forwarding is enabled:
cat /proc/sys/net/ipv4/ip_forward echo 1 > /proc/sys/net/ipv4/ip_forward
- Now you should be able to ping each other between
host1andhost2.
For an example of using this configuration, you may want to try out the OpenFlow NAT Example.
Attachments (6)
- OVS Routing abstract.png (23.9 KB) - added by 10 years ago.
- OVS Routing detail.png (40.1 KB) - added by 10 years ago.
- 2boxes.png (31.4 KB) - added by 10 years ago.
- 2boxes.pptx (20.7 KB) - added by 10 years ago.
- OVS Routing abstract.pptx (20.7 KB) - added by 10 years ago.
- OVS Routing detail.pptx (21.2 KB) - added by 10 years ago.
Download all attachments as: .zip
