| Version 2 (modified by , 8 years ago) (diff) |
|---|
Appendix for the Understanding the AM API using Named Data Networking Exercise
5.2 Visualizing your Named Data Networking (NDN) application using the GENI Desktop
These are instructions for the optional part of the Understanding the AM API using a Named Data Networking application tutorial. Make sure you have completed the instructions at Trying out the NDN Application before you continue.
5.2.1 Launch the GENI Desktop
|

Figure 5-1 Click on the GENI Desktop button in the Slice Tools section of your Slice page. |
|
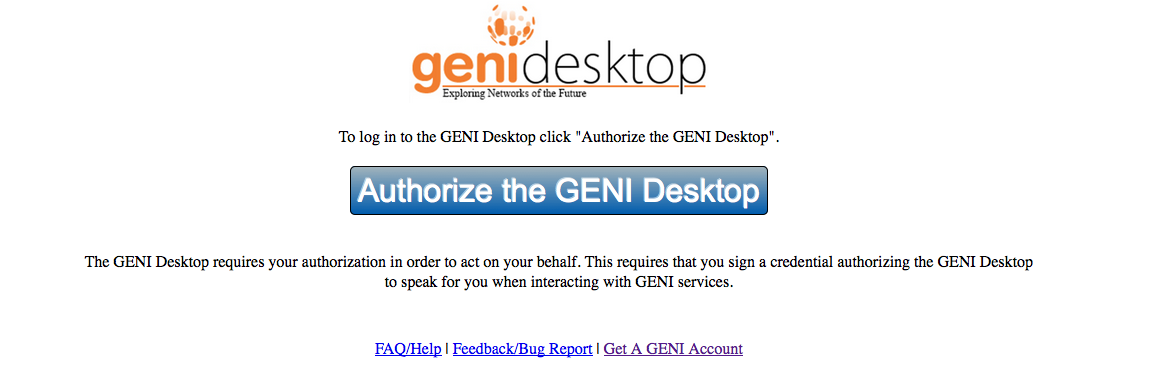
Figure 5-2 Click on the Authorize the GENI Desktop button. |
|
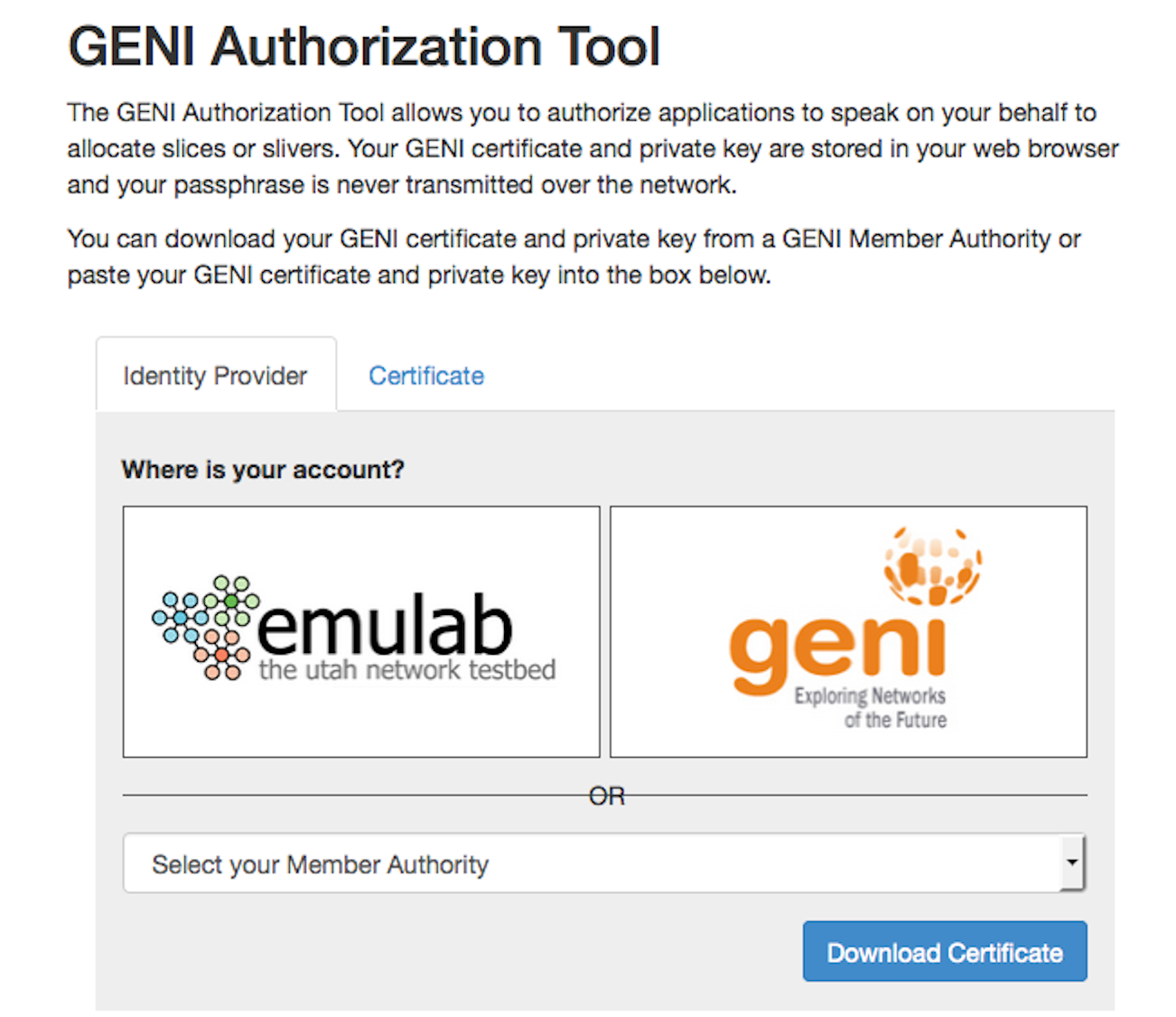
Figure 5-3 Click on your member authority. |
|
|
|

Figure 5-4 GENI Desktop Welcome. |
5.2.2 Setting up the visualization
We are now ready to graph traffic on the four links of the topology.
|

|
|

|
|

|
5.2.3 Visualizing your Experiment
- At this point you will see two graphs showing traffic on each of the links on your experiment. The traffic you see on the links is broadcast traffic from the switch on the rack to which these nodes connect. It is not related to your experiment.
|
- Your graphs should now show traffic on the
lan-1andlan-2links (see example below). The left part of the graphs is the network being quiet, while the spikes on the right are the Interest requests and Data packets. The first spike onlan-2is a request from the Internet-Router node, thus no traffic onlan-1. The same request is made by one of the consumersPIorExperimenter, thus traffic only flows onlan-1. The second spike on both graphs is one of the consumers fetching data from the custodian node. Please take note that the graphs are not scaled for direct comparison and take careful note of whether the max Y values are in bytes or kilobytes.
Cleaning up
Go back to the NDN exercise to free up the resources you used in this experiment.

