This exercise is based on as assignment by Sonia Famy, Ethan Blanton and Sriharsha Gangam of Purdue University.
For this experiment we will run an OpenFlow Firewall.
- Log into switch and run the following commands to download and run the firewall controller:
sudo apt-get install python-pip python-dev libxml2-dev libxslt-dev zlib1g-dev
sudo pip install oslo.config
-
Run a simple learning switch controller:
cd /tmp/ryu
./bin/ryu-manager --verbose ryu/app/simple_switch.py
- Verify simple connectivity by logging into right ping left
ping left
Notice the printouts of the ryu simple switch controller.
-
Stop your controller by Ctrl-c and remove all your flows
sudo ovs-ofctl del-flows br0
- Make your switch into a firewall by downloading and running the appropriate Ryu controller:
wget https://github.com/GENI-NSF/geni-tutorials/raw/master/OpenFlowNetworkDeviceFirewall/gpo-ryu-firewall.tar.gz
tar xvfz gpo-ryu-firewall.tar.gz
cd gpo-ryu-firewall/
/tmp/ryu/bin/ryu-manager simple_firewall.py
WARNING If at some point your controller prints an error, kill it (ctrc-c) and start it again.
- Log into right and run a nc server:
nc -l 5001
- Log into left and run a nc client:
nc 10.10.11.1 5001
- Type some text in left and it should appear in right and vise versa.
- In the terminal for switch you should see messages about the flow being passed or not:
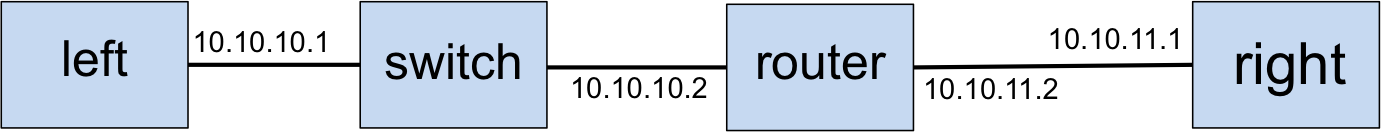
Extracted rule {'sport': '57430', 'dport': '5001', 'sip': '10.10.10.1', 'dip': '10.10.11.1'}
Allow Connection rule {'dport': '5001', 'dip': '10.10.11.1', 'sip': '10.10.10.1', 'sport': 'any'}
- CTRL-C to kill nc in each terminal.
- Run a nc server on port 5002, then 5003.
- Compare the observed behavior to the contents of ~/gpo-ryu-firewall/fw.conf. Does the behavior match the configuration file?
- Stop the Firewall controller and run a simple switch controller. Is there any traffic being blocked now? Don't forget to delete the flows after you stop the controller
- Feel free to modify the configuration file to allow more traffic.
|