| Version 13 (modified by , 7 years ago) (diff) |
|---|
Intro to OpenFlow Tutorial (OVS)
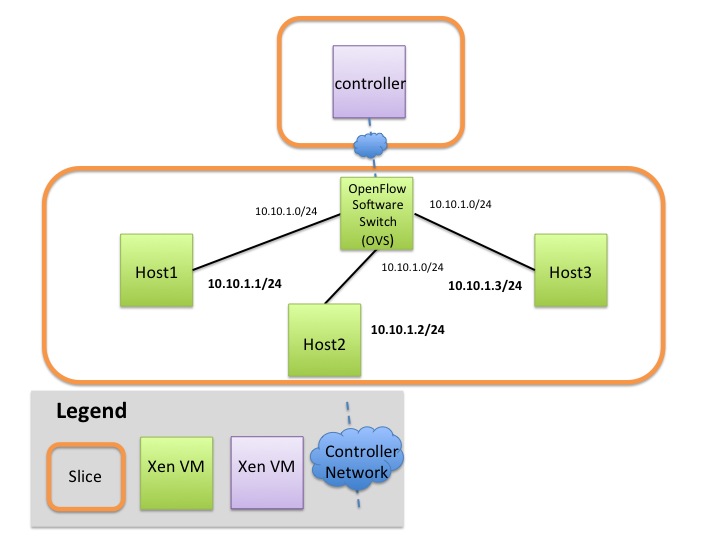
| Overview In this tutorial we are going to use Open vSwitch (OVS) as an OpenFlow switch connected to three hosts. OVS is a software switch running on a compute resource. The other three hosts can only communicate through the OVS switch. The experiment will need (the rspecs for this exercise are provided later in this section):
|
Step 1. Obtain resources
For the following reservation you can use any aggregate.
| |
You can use compute resources from any InstaGENI rack and any reservation tool (Portal, jFed, Omni, etc) For a list of available InstaGENI racks see the GENI Production Resources page. |
- Reserve a VM that runs your OpenFlow controller.
RSpec: You can use the following url, url: http://www.gpolab.bbn.com/experiment-support/OVSFloodLight/ControllerCustom_request_rspec.xml
- Reserve your network, that includes a VM with OVS installed.
RSpec: You can use the following url, url: http://www.gpolab.bbn.com/experiment-support/OVSFloodLight/OVS_TPOLOGY_request_rspec.xml
| |
You will need SSH access to your nodes. If you don't know how to SSH to your reserved hosts learn how to login |
Step 2. Configure the Open vSwitch
Overview:
Although OVS is installed and initialized on the host that is meant to act as a software switch, it has not been configured yet.
There are two main things that need to be configured:
(1) configure your software switch with the interfaces as ports and
(2) point the switch to an OpenFlow controller.
2a. Configure the Software Switch (OVS Window)
- Login to the OVS host
- Create an Ethernet bridge that will act as our software switch:
sudo ovs-vsctl add-br br0
- Prepare the interfaces to be added as ports to the OVS switch
- Your OVS bridge will be a Layer 2 switch and your ports do not need IP addresses. Before we remove them let's keep some information
- Run
ifconfig - Write down the interface names that correspond to the connections to your hosts. You will see three interfaces with IP's 10.10.*.*, one for each host. These are the data plane interfaces.
- Remove the IP from your data interfaces.
 Be careful not to bring down eth0. This is the control interface, if you bring that interface down you won't be able to login to your host. For all interfaces other than
Be careful not to bring down eth0. This is the control interface, if you bring that interface down you won't be able to login to your host. For all interfaces other than eth0andl0(your interface names may vary) run :sudo ifconfig ethX 0 sudo ifconfig ethY 0 sudo ifconfig ethZ 0
- Run
- Your OVS bridge will be a Layer 2 switch and your ports do not need IP addresses. Before we remove them let's keep some information
- Add all the data interfaces to your switch (bridge).
 Be careful not to add interface eth0. This is the control interface. So now that we know the names of our three 10.10.*.* interfaces, we can add them as ports to our bridge. These three interfaces are your data interfaces.
Be careful not to add interface eth0. This is the control interface. So now that we know the names of our three 10.10.*.* interfaces, we can add them as ports to our bridge. These three interfaces are your data interfaces.
sudo ovs-vsctl add-port br0 ethX sudo ovs-vsctl add-port br0 ethY sudo ovs-vsctl add-port br0 ethZ
- Trust but verify. Congratulations! You have configured your software switch. To verify the three ports configured run:
sudo ovs-vsctl list-ports br0
2b. Point your switch to a controller
| |
An OpenFlow switch will not forward any packet unless instructed by a controller. Basically the forwarding table is empty, until an external controller inserts forwarding rules. The OpenFlow controller communicates with the switch over the control network and it can be anywhere in the Internet as long as it is reachable by the OVS host. |
- Login to your controller
- Find the control interface IP of your controller, use ifconfig and note down the IP address of
eth0. - In order to point our software OpenFlow switch to the controller, in the ovs terminal window, run:
sudo ovs-vsctl set-controller br0 tcp:<controller_ip>:6653
- Set your switch to
fail-safe-mode. For more info read the standalone vs secure mode section. Run:sudo ovs-vsctl set-fail-mode br0 secure
- Trust but verify. You can verify your OVS settings by issuing the following:
sudo ovs-vsctl show
2c. standalone vs secure mode
The OpenFlow controller is responsible for setting up all flows on the switch, which means that when the controller is not running there should be no packet switching at all. Depending on the setup of your network, such a behavior might not be desired. It might be best that when the controller is down, the switch should default back to being a learning layer 2 switch. In other circumstances however this might be undesirable. In OVS this is a tunable parameter, called fail-safe-mode which can be set to the following parameters:
standalone[default]: in this case OVS will take responsibility for forwarding the packets if the controller failssecure: in this case only the controller is responsible for forwarding packets, and if the controller is down all packets are dropped.
In OVS when the parameter is not set it falls back to the standalone mode. For the purpose of this tutorial we will set the fail-safe-mode to secure, since we want to be the ones controlling the forwarding.
