| Version 14 (modified by , 12 years ago) (diff) |
|---|
Network Security and Traffic Analysis
The GENI network infrastructure enables security research that has not been possible before due to potential disruption to production networks. This project includes a number of security and privacy experiments that include:
-WiMAX DDoS analysis with analysis of variance finding vulnerable control parameter settings;
-Privacy/Anonymity side-channel Hidden Markov Models (HMMs) will be inferred to break anonymity systems;
-DDoS traffic measurement to map attack severity vs. network topology;
-Side-channel vulnerability removal protocol tested at scale; and
-DDoS countermeasure testing to neutralize DDoS attacks
Institution(s)
Clemson University
Team Members
- Prof. Richard R Brooks <rrb@acm.org>, principal investigator
- Prof. Kuang-Ching Wang <Kuang-Ching Wang>, co-principal investigator
- Ilker Ozcelik <iozceli@g.clemson.edu>, PhD candidate
- Katherine Cameron, <kccamer@g.clemson.edu>, Master's student
- Lu Yu, <lyu@clemson.edu>, PhD candidate
Project Team
Experiments
WiMAX Bandwidth Contention Process and DDoS
Our WiMAX research involves analyzing the cross-layer affects of the system parameters used for the Bandwidth Contention Process. We are specifically looking at how these parameters affect a subscriber station's (SS) throughput, packet loss rates, and vulnerability to Distributed Denial of Service (DDoS) attacks. Software simulations using the NS-2 simulator manipulated three system parameters for a set of SS that included client and attacker SS's. Attacker SS's system parameters and client SS's system parameters were treated separately, giving a total of six parameters. The parameters, request retires, backoff start, and frame duration, were set to a low, medium, and high value within their respective range. Seven replications of each combination of parameter settings were conducted and ANOVA analysis indicates that frame duration and request retries plays a significant role in SS's throughput. For software simulation results please see:http://www.clemson.edu/~rrb/WiMax/WiMaxDDoSTest.tgz
We are now using ORBIT, hosted by Rutgers University's WINLAB and part of the GENI network, to conduct hardware experiments using real WiMAX equipment. We are replicating the above software experiments to verify software simulation results, analyze the validity of the NS-2 WiMAX simulator, and gain further information about the cross layer affects of the system parameters used in the Bandwidth Contention Process. Currently our hardware experiments are configured with eight SS nodes, a sink node, and 1 base station (BS). In the future we hope to extend the number of SS used in our experiments. We are using the resource of sandbox 4 and the outdoor sandbox. The indoor sandbox creates a controlled environment for wireless experiments and outdoor consists of an outdoor BS and nodes that vary in geographical location. Are hardware experiments manipulate two system parameters, backoff start and backoff end. Frame duration is not considered, because all WiMAX equipment currently manufactured supports only 5ms frame duration. Data will be collected for two replications of each combination of parameter settings. When the data collection is complete, analysis will be carried out to determine the affect of system parameters on real WiMAX hardware.
Performance Analysis of DDoS Detection Methods on Real Network
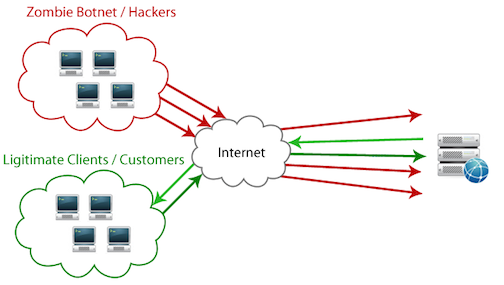
DDoS attacks attempt to make a computer resource unavailable to its legitimate users. DDoS occurs when a set of nodes flood the network to consume the resources of the target. These nodes are compromised by an attacker and become zombie agents in a bot net. Most of the time the owners don’t know that they are part of a bot net. The compromised systems send dummy traffic/requests to the target system after receiving a remote command. The distributed structure of the attack makes it difficult to distinguish attack traffic from the legitimate traffic. Thus it is not possible to identify the attack and react quickly, as a sudden increase of interest to a certain website may also give a similar effect; known as Slashdot effect.
Figure 1 - DDoS Attack
In addition to the complexity of the problem, the complexity of the Internet makes analysis even more challenging. We mostly verify theoretical studies using computer simulations and not by using the real Internet and its data. Unfortunately network traffic, one of the most important parameters which is used for DDoS detection routines, cannot be accurately generated because of its unpredictable characteristic.
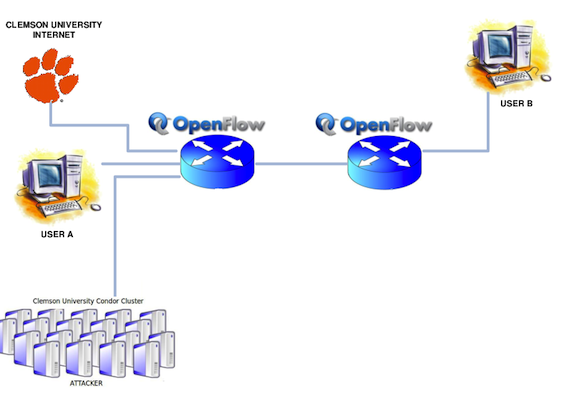
In this study, we propose and design an experiment setup to collect Internet traffic time-series and evaluate real performance of DDoS detection methods using real network and real Internet traffic without jeopardizing the original network. In our study, we use the same setup to collect time-series and test existing DDoS detection methods. The experiment setup is Figure 2.
Figure 2 - Experiment Setup
Our experiment has two main goals. These are: collecting time-series from Internet traffic to use in the future experiments and verifying the performance of DDoS detection methods which are optimized by using computer simulations.
Data Collection
In order to collect time-series from internet traffic, we use switch statistic request messages at the controller. Number of packets time-series collected from Clemson University campus network can be seen in Figure 3.
Figure 3 - Clemson Uni Traffic
Verifying DDoS Detection Methods
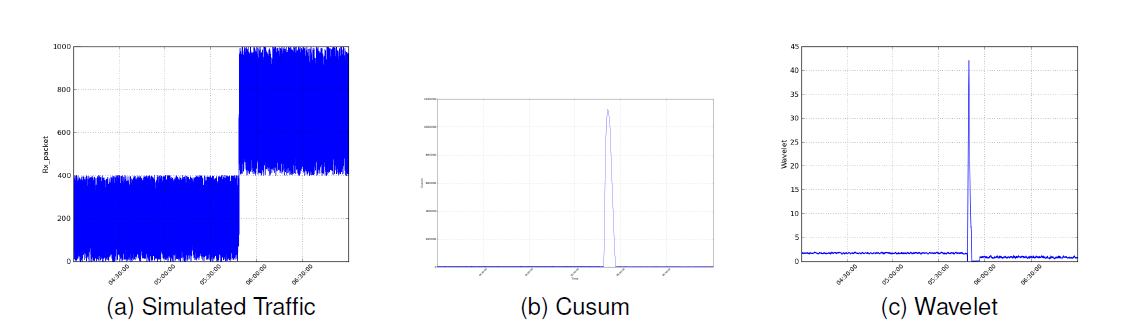
We are currently working on the change point detection using non-parametric Cu-sum based and Wavelet methods. These methods detect the anomalies on the observations in an observation window. Results we obtained from computer generated data, its cu-sum ,wavelet and real Internet traffic, its cu-sum, wavelet are shown in Figure 4 and Figure 5 respectively.
Figure 4 - DDoS detection using Cu-sum and Wavelet methods in computer generated data
Figure 5 - DDoS detection using Cu-sum and Wavelet methods in real Internet traffic
Publications
- I. Ozcelik and R. Brooks, “Security experimentation using operational systems,” in 7th Annual Cyber Security and Information Intelligence Research Workshop, October 2011.
- Juan Deng, Richard R. Brooks, and James Martin, “Assessing the Effect of WiMAX System Parameter Settings on MAC-level Local DoS Vulnerability”, International Journal of Performability Engineering, 8 (2) 163-178, (2012)
Previous Students and Degrees
- Deng, Juan, Ph. D., 2011, Thesis: Connected Vehicle Information Assurance
New Arrivals
- Ms. Deng became the proud mother of this darling baby boy during her work on this project.
Acknowledgements
We would like to express gratitude to the National Science Foundation (NSF) for supporting this research. The research is supported by NSF under Grant No. 1049765. Any opinions, findings, and conclusions or recommendations expressed by this research or related material are those of the author(s) and do not necessarily reflect the views of the National Science Foundation.
Attachments (9)
- Brooks.jpg (16.4 KB) - added by 12 years ago.
- ResearchGroup.jpg (55.2 KB) - added by 12 years ago.
- Figure1.png (72.6 KB) - added by 12 years ago.
- Figure2.png (116.0 KB) - added by 12 years ago.
- Figure3.png (135.0 KB) - added by 12 years ago.
- Figure4.png (42.2 KB) - added by 12 years ago.
- Figure5.png (40.2 KB) - added by 12 years ago.
- JuanBaby.jpg (25.6 KB) - added by 12 years ago.
- Poster_GEC15.pdf (1.2 MB) - added by 12 years ago.
Download all attachments as: .zip